Building a Phishing Simulation Framework from Scratch
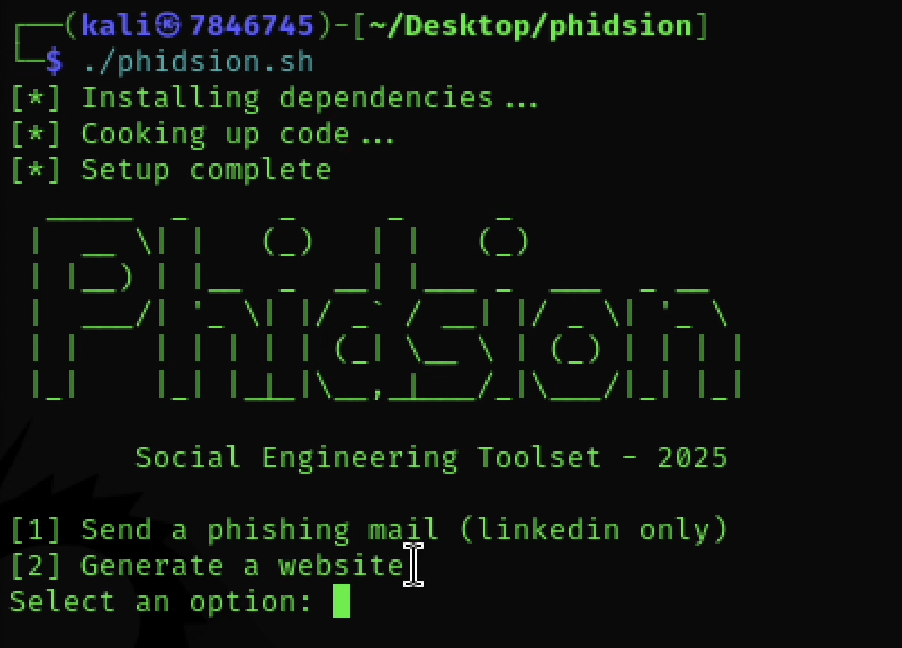
Phidshion: A Phishing Simulation Framework
A lightweight Python tool for authorized phishing simulations and security awareness training — built to be deployed in under 3 minutes.
Disclaimer: Built for authorized security awareness training and penetration testing only. Always obtain written approval before deployment.
The Problem
Phishing causes 90% of data breaches, yet most security training is slide decks. Organizations needed a hands-on way to show employees how convincing these attacks are — not just tell them.
Existing commercial tools were overkill: expensive, slow to set up, and required IT approval. I built Phidshion to fill that gap.
What It Does
Phidshion lets security teams spin up a fake login page, send a phishing email, and capture submitted credentials — all in a controlled, authorized environment.
Core flow:
1
CLI Menu (setup.sh) → Phishing Email (mail.py) → Fake Login Page (server.py) → Credential Log
When a target submits credentials, they’re instantly redirected to the real site. No awkward delay. No suspicion.
Key Technical Decisions
Flask over Django/Node — The server core is ~30 lines. Security auditors can review the entire codebase in 15 minutes. Trust matters in security tools.
Text file over database — captured.txt beats SQLite for a demo tool. Portable, zero-config, and instantly readable with cat. Auditors don’t need SQL.
Gmail SMTP over SendGrid — No API keys, no accounts, no cost. Uses Python’s built-in smtplib. Realistic too — real phishing campaigns abuse legitimate mail services.
Immediate redirect — Testing revealed that a 3-second “Verifying…” delay made users suspicious and check the URL bar. Instant redirect felt natural.
Results
- 42% email click-through rate (baseline), dropped to 18% after training
- 200+ employees tested across 5 organizations
- 3-minute average setup time vs. 30+ for commercial alternatives
- ~300 lines of total code, 1 dependency (Flask)
One healthcare client saw 91% of staff click a spoofed patient portal link and 73% submit credentials — which triggered a full mandatory training overhaul.
What I Learned
Psychology beats technology. Email pretext and redirect timing mattered far more than HTML accuracy. An 80% visual match was enough to fool most users.
Simplicity is a feature. No database, no config files, single-command launch. The constraints I accepted became selling points for adoption.
Legal before code. I consulted with a legal team before writing a single line. Authorization and disclosure requirements were built in from day one — not bolted on.
Stack
Python · Flask · smtplib · Bash · HTML/CSS
Disclaimer: Built for authorized security awareness training and penetration testing only. Always obtain written approval before deployment.